It’s late January 2012. Governments all over the world are considering signing up to a new US-led trade proposal intended to curtail copyright violation, the Anti-Copyright Trade Agreement (ACTA). There have been widespread protests, on and offline: the loose-knit collective of activists, hackers and internet denizens of all stripes known as ‘Anonymous’ believe ACTA represents an attempt by governments to limit and control the core freedoms of the internet, in particular the massive cultural exchange of ideas and information made possible by file-sharing online.
In Poland, the agreement has already been signed off; all that is needed for it to be adopted into law is a majority vote in parliament. The government website is offline, taken down by a distributed denial of service (DDoS) attack launched by Anonymous, which sends a message to politicians who are considering voting in favour. By the final week of January, over 10,000 people gather in Krakow in a last-ditch protest to influence the vote.

Members of the Palikot Movement Party protest against the ratification of the Anti-Counterfeiting Trade Agreement
And then something unexpected happens: on 26 January 2012, while casting their votes in parliament, some members of the Polish government conceal their faces with paper Guy Fawkes masks. The mask, by now the signature icon for Anonymous, has become common protest regalia among rabble-rousers across the globe, from Egypt’s Tahrir Square to London’s Occupy protests. But this is the first case of public servants adopting the symbol. The image is circulated far and wide on social media platforms. Although Polish politicians used it to launch a specific protest against ACTA, the gesture and its photographic memorialisation worked in a much broader capacity to legitimate Anonymous. ‘These parliamentarians were wearing Anonymous Guy Fawkes masks,’ one Anonymous activist blogged, ‘while the parliament’s website was down due to DDoS by Anonymous. We can’t emphasise that point enough – this is a game-changer.’
Less than a month later a very different image of Anonymous was circulated. On 21 February 2012, the Wall Street Journal reported that General Keith Alexander, the director of the United States National Security Agency (NSA), had briefed officials at the White House in secret meetings, claiming Anonymous ‘could have the ability within the next year or two to bring about a limited power outage through a cyberattack’. So only weeks after the ‘game changer’, the group was described as an imminent and credible threat.
The ‘ability’ to bring about a power outage was undefined. Could it mean that hackers had already acquired passwords that would give them access to power facilities? Or was the warning based on information supplied by an informant who had been working with Anonymous? Either way, General Alexander’s claims were frightening and bold, as well as vague. An attack on the power grid systems would cause havoc and potentially even threaten lives.
It is unlikely that we will ever find out whether the NSA assessment was based on credible intelligence or whether it was simply meant to smear and discredit Anonymous. Further news reports quoted activists and security experts and dismissed NSA claims as ‘fear-mongering’. The group, for all its varied tactics, both legal and illegal, has to date never been known to publicly call for such an attack – and there is no evidence to suggest that it would so much as consider it. A tactic like this would be very out of character for the collective, which, though often subversive, generally conforms to ethical norms and defends civil liberties.
While Anonymous has never occupied a controversy-free place on the world stage, by February 2012 it began to be portrayed as an open source brand of radical protest politics and not necessarily as hooligans hell-bent on unleashing extremist, chaotic acts like taking down power grids. More significantly, while the name has been used to pull together a range of unrelated causes, from environmental rights to snuffing out paedophilia rings, Anonymous activists are most effective and forceful when fighting censorship.
With campaigns like Operation Payback, which targeted corporations like MasterCard when it stopped providing services to WikiLeaks, OpTunisia, which responded to Tunisian government tactics against protesters and journalists, and OpJapan and OpMegaupload, launched in response to proposed copyright legislation, it is when Anonymous activists defend the internet’s core freedoms and expose the shadowy workings of state and corporate surveillance that it has the most impact. The NSA news story about the exigent threat from Anonymous failed to gain traction in the public consciousness. Perhaps it would have if it had come earlier, for instance between May and July 2011, at the height of attacks led by Lulzsec.
Anonymous launched Operation Megaupload
In contrast to most Anonymous actions, Lulzsec, a break-away hacker group, acted whimsically, its hacks not always tethered to a political issue. Lulzsec sometimes hacked to make a political statement and, in other instances, for lulz, internet slang for laughs. During this period, media attention, which was colossal, was most heavily focused on Anonymous as hackers rather than as a general protest group. Activities under the Anonymous banner, such as those of Lulzsec, show that even though Anonymous has gained a measure of respect because it champions free speech and privacy causes, it is also notorious for its irreverent and controversial approach to dissent.
To be sure, most of its activities are legal, but a small subset of tactics – such as DDoS attacks and hacking – are illegal, a criminal offence under all circumstances. These tactics also score the most headlines. Some, like ‘doxing’ (the leaking of personal, sensitive information, such as social security numbers and home addresses), reside in a legal grey zone because mined information is found on publicly accessible websites. During the course of a single operation different participants might deploy all three modes – legal, illegal and legally grey tactics.
Take Operation Bart, in August 2011. Anonymous focused on getting the word out when San Francisco Bay Area Rapid Transit (BART) officials disabled mobile phone reception on station platforms to thwart planned anti-police brutality protests. Soon after, Anonymous helped organise street demonstrations. But a couple of individuals also hacked into BART’s computers and released customer data in order to garner media attention – at least that’s how one participant explained the incident to Amy Goodman on television and radio programme Democracy Now. Someone also found a racy, semi-nude photo of BART’s official spokesperson Linton Johnson on his personal website, which was then republished on the ‘bartlulz’ website with considerable fanfare, along with the brazen rationalisation: ‘if you are going to be a dick to the public, then I’m sure you don’t mind showing your dick to the public.’
During the course of an operation, vulnerability and weakness is often identified and exploited. These sorts of actions provoke controversy (even within Anonymous) and also find their way into headlines, boosting the group’s public profile. At times, members of the loose collective are purposely deceitful and propagate false information about their activities. This can be a tactic for self-protection in some cases, and in other cases an antic to coax headlines out of the media, which can be somewhat enamoured with hacking.
Antisec, one of the more well-known hacker groups affiliated with Anonymous, might claim an exploit without having actually been involved in the activity. Hackers will often rely on botnets – networks of compromised computers – to momentarily knock a website offline, but won’t advertise this fact in press releases. Between 10 and 11 September 2012, for instance, Antisec claimed to have procured 12 million unique device identification numbers from Apple iOS devices by hacking into an FBI agent’s laptop computer. As it turns out, while the identification numbers were verified, the source turned out to be an iPhone and iPad app developer, Blue Toad. Because tactics range from the frivolous to the controversial to the illegal and because it has been known to generate hype around its own activities, it can be easily targeted itself. Obfuscation and deceit contributes to Anonymous’s mystique and its power, but also makes it vulnerable to misinformation campaigns spread by others.

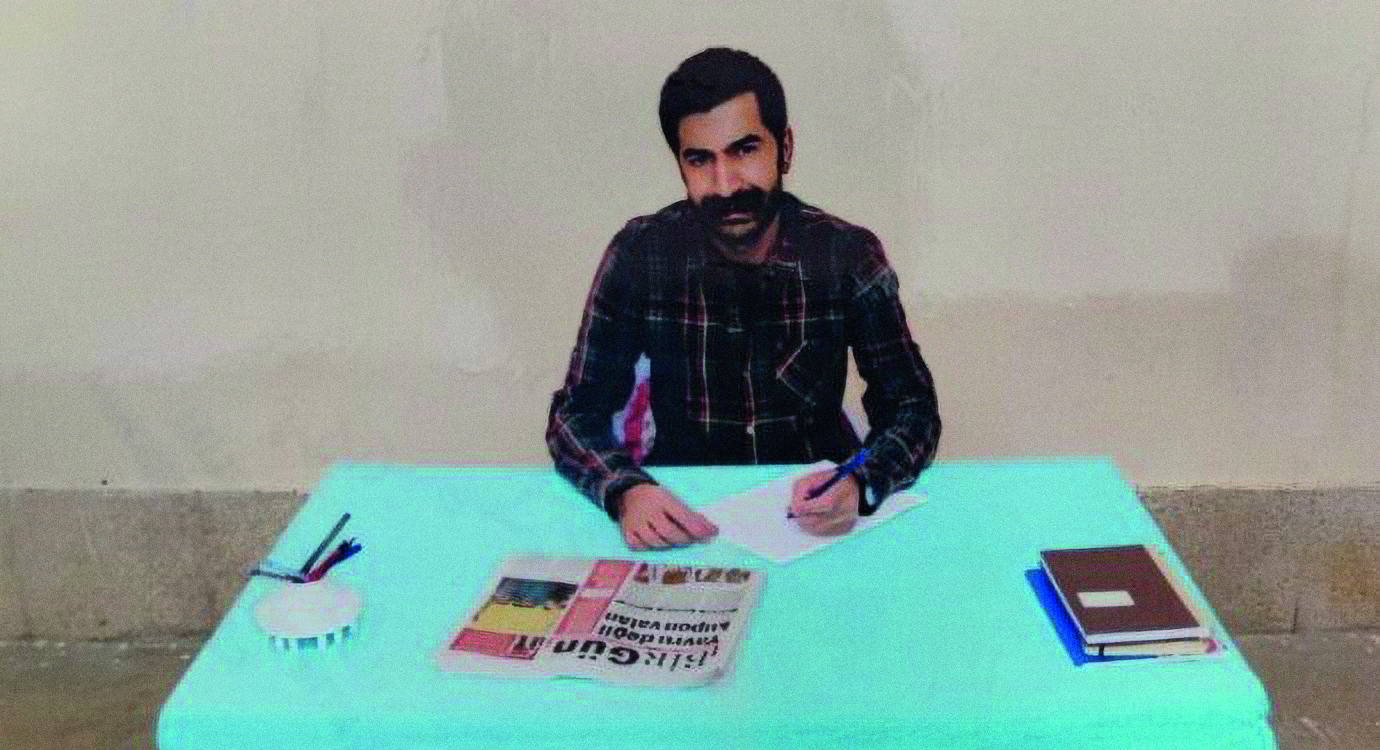
Antisec – One of the more well-known hacker groups affiliated with Anonymous
The biggest lesson that can be learned from Anonymous is that the internet will judge – often quite swiftly – the actions of individuals, corporations and governments. And by the internet I mean the countless hackers and geeks from São Paulo to Sydney who understand how the web works, a smaller class who know how to subvert routers and protocols, and a larger number who will rally when the internet and values associated with it are in danger.
This is not to say that every geek and hacker supports Anonymous. In fact, many rather dislike it or its controversial tactics, such as DDoS; some hackers are resolute and unyielding in their view that DDoS is a species of censorship in itself. There are also many different ways to defend the internet, such as writing open source software or joining the Pirate Party. Anonymous is a distinct, emerging part of this diverse and burgeoning political landscape. Its real threat may lie not so much in its ability to organise cyberattacks but in the way it has become a beacon, a unified front against censorship and surveillance.
It might be best thought of as the irascible and provocative protest wing of the internet’s nascent free speech and privacy movement. Though it works to publicise specific issues at the most inconvenient time for the individual, group or company being exposed, it also brings into sharp focus an important trend, dramatising the value of privacy and anonymity in an era where both are rapidly eroding.
Anonymous, of course, champions anonymity, and this is echoed in both the iconography associated with it and its ethical codes. Seeking individual recognition and especially fame is taboo, for example; you are expected to do work for the team, not for one’s own personal benefit or status. The movement, therefore, provides a rare countermeasure in deeds, words and symbols against a world that encourages people to reveal their lives, where the internet remembers everything about us, where our histories are permanently stored in search indexes and government databases – and at a time when governments’ ability to surveil its citizens has grown exponentially thanks to low-cost, ubiquitous digital technologies and new public-private partnerships.
However explosive Anonymous is today, its continued presence on the world stage is certainly not guaranteed to last. It is plagued by infighting, fragmentation, as well as brand fatigue. Paranoia exploded in spring 2012 after the news broke that Hector Xavier Monsegur, known more commonly by his hacker handle ‘Sabu’, had been exposed as an FBI informant. Most troubling for its long-term survival is government crackdown: since summer 2011, over 100 alleged participants have been arrested around the globe, from Romania, Turkey, Italy, the UK, the US, Chile and Germany. But even if the loose-knit collective fades away, irreverent political protest on the internet is unlikely to end.
Since 2008, when individuals started to organise diverse collective actions under the banner of Anonymous, a living model was created, demonstrating to the world what a radical politics of dissent on the internet looks like. Even if Anonymous was to vanish, its history, exploits and propaganda material are here to stay; there will likely be others — in different forms and with distinct twists — who will take its place.
What is a little less clear is what will eventually become of freedom of expression online, given the increasing capabilities for surveillance, censorship and control all over the world. Is Anonymous merely the party at the funeral of online freedom? Or does it represent the irreverent clowns, rabble rousers, and tricksters who are keeping the reaper at bay and enabling others, from protesters on the street to elected representatives in parliament, to join the raucous political carnival and challenge threats to personal privacy and freedom?
Gabriella Coleman is Wolfe Chair in Scientific and Technological Literacy at the Department of Art History and Communication Studies at McGill University. She tweets from @BiellaColeman